
A Secure Way to Share Passwords Without the Risk
Share
Let's be honest, sharing a password over text or email feels like the quickest, simplest solution. But that convenience is a smokescreen for a serious security gamble, making these common habits a terrible choice for securely sharing passwords. What feels like a simple action can easily become a major vulnerability for your personal and business data.
The Hidden Dangers of Common Password Sharing Habits
We’ve all done it. You text the Wi-Fi password to a guest or email login details to a new team member. The impulse makes sense—we're wired for convenience. The problem is, this is exactly what cybercriminals are banking on. Channels like email, messaging apps, and even shared spreadsheets are rarely encrypted and create a permanent, searchable record of your most sensitive credentials.
This casual approach leaves a digital breadcrumb trail that’s frighteningly easy to follow. If a hacker gets into your email account, all they have to do is search for "password" or "login" to hit a potential goldmine. This isn't just a hypothetical scenario; it was a key factor in the notorious 2014 Sony Pictures hack. Attackers found passwords stored in plain text within spreadsheets and emails, allowing them to gain deeper access and inflict massive damage.
Why We Choose Convenience Over Caution
The psychology here is pretty straightforward. The immediate need for access always feels more urgent than the abstract threat of a future data breach. We work on a basis of trust, assuming the person on the other end will handle the information with care.
But that trust doesn't extend to the channels we're using. A password is only as secure as the method used to send it, and our everyday digital communication tools just weren't built for secrecy.
The consequences of poor password security are staggering. In just the first half of a recent year, an incredible 3.8 billion credentials were leaked, with a password being cracked roughly every second. To make matters worse, about 88% of these were under 12 characters long, highlighting how weak passwords amplify the risk of insecure sharing. You can dig deeper into these figures by checking out the latest password security statistics.
Visualizing the Risk
Take a look at the image below. It shows the interface of a typical password manager, a tool designed from the ground up to prevent the very risks we're talking about.

This kind of organized, encrypted vault is the polar opposite of scattering your credentials across insecure platforms. Realizing that your current habits might be putting you at risk is the first, most important step toward adopting a truly secure way to share passwords and safeguard your digital life.
When it comes to sharing passwords securely, let's be honest: all credible advice points in one direction. You need a dedicated password manager. These tools aren't just a good idea; they're the gold standard for a reason.
Password managers are purpose-built to handle sensitive data. They wrap your credentials in powerful, end-to-end encryption, which means the information is scrambled the instant it leaves your device and only becomes readable again when it reaches the person you authorized. No one in between—not your ISP, not a hacker on the Wi-Fi, not even the password manager company itself—can decipher it.
Think of it less like an email and more like an armored truck for your digital keys. Sending a password in a text message is like mailing cash in a plain envelope. Using a password manager is like locking that cash in a vault that only the intended recipient has the key to open. It completely changes the game by sidestepping the massive risks of manual sharing.
How Shared Vaults Work
The magic behind secure sharing in a password manager is the shared vault (sometimes called a collection or shared folder). It's a secure, encrypted container where you can place specific logins meant for a team, your family, or a particular project. Instead of passing around individual passwords, you're creating a controlled space for a whole set of credentials.
Let's say your marketing team needs access to the company's social media profiles. The old, insecure way involved a spreadsheet or a messy email chain. The right way looks like this:
- You create a new vault and name it something like "Marketing Social Accounts."
- Inside, you add the logins for your company's Twitter, LinkedIn, and Facebook pages.
- Then, you simply invite your team members to that specific vault.
Just like that, everyone on the team can access the accounts they need directly from their own password manager. The best part? They can log in without ever seeing the actual passwords written out.
Getting Specific with Access Control
This is where password managers truly shine. You get granular control over who can do what. Not everyone on a team needs full, unrestricted access to every password, and a good password manager lets you reflect that reality.
You can typically assign specific roles to each person, giving you fine-tuned command over your credentials. Common permission levels look something like this:
- View-Only or "Can Use": The person can use the credential to log in (often via a browser extension) but can't see, copy, or reveal the actual password. This is perfect for interns or temporary contractors.
- Edit Access: This user can see, use, and update the password. It’s a great fit for a team lead who might need to change a password and have it sync for everyone else.
- Admin Access: This role gets the keys to the kingdom. They can edit passwords and manage who has access to the vault by adding or removing users.
This approach lets you enforce the principle of least privilege—a cornerstone of good security. You're only giving people the bare minimum access they need to do their job, which dramatically shrinks your risk of data exposure, whether it's accidental or malicious. For a deeper dive, check out our guide on secure password sharing tips and tools.
By moving all your shared credentials into an encrypted, access-controlled vault, you instantly break the dangerous habit of sending passwords through insecure channels. You establish a single, reliable source of truth that is both incredibly convenient and heavily fortified. It’s the modern, practical answer to a very old problem.
Choosing the Right Password Manager for Your Needs
Picking the right password manager isn't a one-size-fits-all deal. The best tool for a family sharing a Netflix login is worlds apart from what a small business needs to manage sensitive client accounts. While the goal is always security, the features that make that security work for you depend entirely on your situation. Honestly, this is the most important step in finding a truly secure way to share passwords that you'll actually stick with.
The first thing I always tell people is to think about who you're sharing with. Is it just you and your partner? Are you coordinating with a small team of 5? Or are you rolling out a solution for a company of 500? The answer completely changes which features you should care about.
For instance, a family plan probably just needs to be simple, sync flawlessly between phones and laptops, and be affordable. A business, however, needs the heavy-duty stuff: detailed security logs, strict user permissions, and ways to enforce company-wide policies.
Core Features to Compare
No matter who you are, there are a few non-negotiable features every good password manager needs for secure sharing. Think of these as the absolute baseline.
- Cross-Platform Sync: The tool has to work everywhere you do—Windows, macOS, iOS, Android, you name it. A password you can't access when you need it is a useless password.
- Robust Browser Extensions: Let's face it, most of our logins happen in a browser. A solid extension that autofills credentials is a game-changer. It means no more risky copy-pasting, which makes being secure almost effortless.
- Multi-Factor Authentication (MFA): The password manager itself must be protected by MFA. This is your vault's last line of defense. Even if someone got your master password, MFA would stop them in their tracks.
This next image really drives home why this is so critical. It highlights the staggering rate of security breaches caused by people reusing the same old passwords and, frankly, the shockingly low number of people using the very tools designed to prevent it.
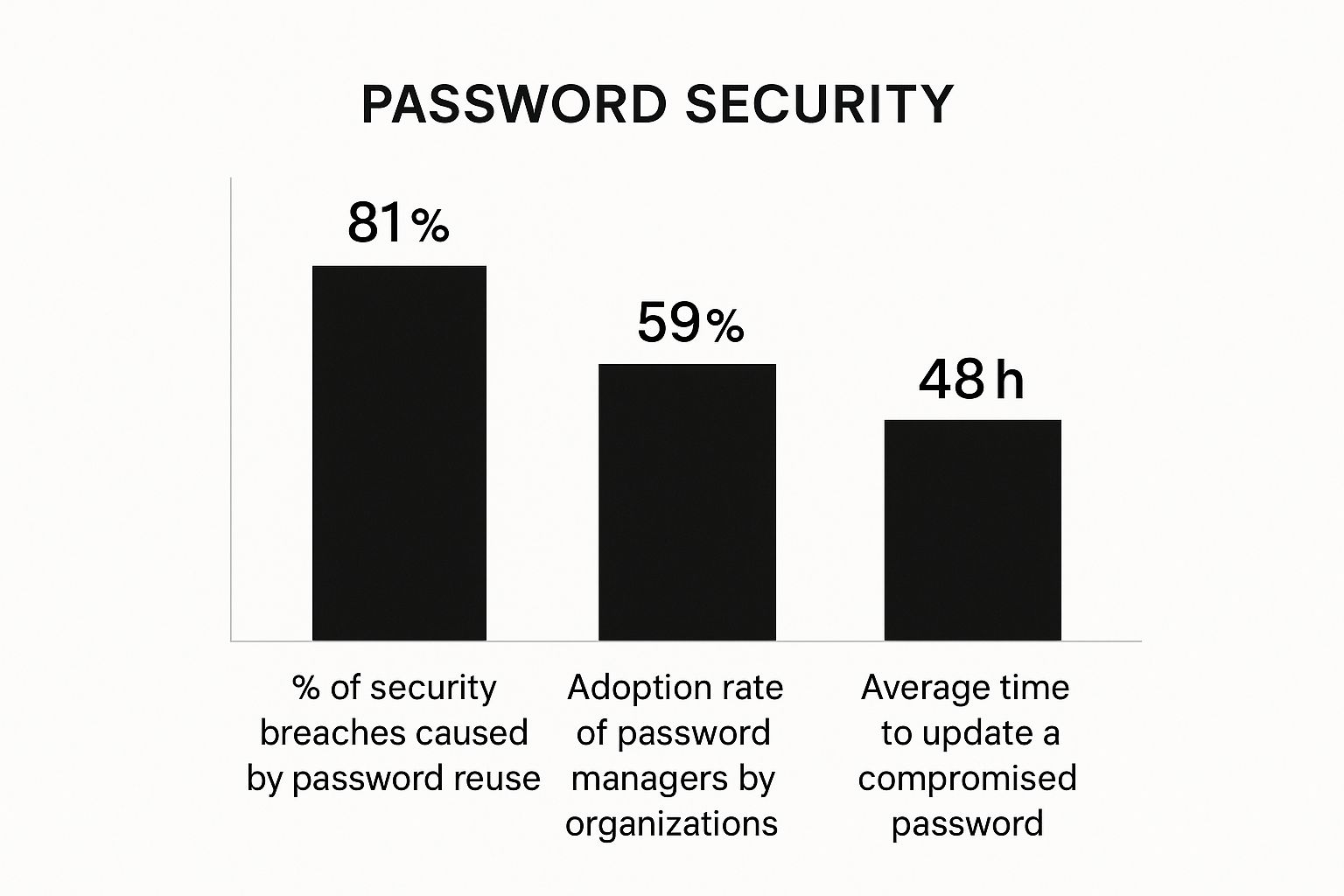
The data is pretty clear: password reuse is a massive vulnerability, yet many teams haven't adopted a password manager, leaving a huge security hole wide open.
Advanced Needs for Business and Teams
If you're picking a tool for your business, the checklist gets longer. You'll want to look for an administrator dashboard. This is your command center, where you can see every shared credential and manage who has access to what, all in one place.
The ability to generate security reports is essential for any business. These audits are your best friend for flagging weak or reused passwords, tracking access, and giving you a clear paper trail for compliance.
Here are a few more business-focused features I always look for:
- Security Audit Logs: You need a crystal-clear record of every action—who viewed a password, who edited it, and when. It's invaluable for tracking down issues or investigating a security incident.
- Granular Permissions: Not everyone needs full control. The ability to set "view-only" versus "edit" rights for each password and each user is crucial. It's the best way to enforce the principle of least privilege.
- Automated User Provisioning: When someone joins the company, they need access. When they leave, that access must be cut off immediately. Automating this process closes a major security gap that often gets overlooked.
When you're trying to decide, it really helps to lay out what matters most for your specific use case. This table breaks down the key features and why they're important for different sharing scenarios.
Password Manager Feature Comparison
| Feature | Why It's Important for Secure Sharing | Example Scenarios (Family, Team, Enterprise) |
|---|---|---|
| Shared Vaults/Folders | Allows grouping passwords for specific projects or people, keeping access organized and preventing accidental oversharing. |
Family: "Streaming Services" vault. Team: "Social Media Accounts" folder. Enterprise: "Client Database" vault for the engineering department. |
| Granular Permissions | Enforces the principle of least privilege by letting you set view-only, edit, or admin rights for each user and each credential. |
Family: Kids can view the Wi-Fi password but not edit it. Team: A contractor can view a login but not share it. Enterprise: Only team leads can edit credentials. |
| Security Audit Logs | Provides a clear, time-stamped record of who accessed or modified a password, which is essential for accountability and compliance. |
Family: Not typically needed. Team: Check who last used the company Twitter login. Enterprise: Provide audit trails for SOC 2 or HIPAA compliance. |
| Emergency Access | Designates a trusted person who can request access to your vault in an emergency, preventing you from being permanently locked out. |
Family: A spouse can access financial accounts if one partner is incapacitated. Team: A manager can access a critical system if an employee is on leave. Enterprise: Not typically used; access is managed via admin roles. |
Ultimately, choosing the right manager means taking a hard look at its capabilities and matching them to your real-world needs. Taking the time to do this homework doesn't just give you better security—it gives you peace of mind.
For a deeper dive into this topic, you can explore our guide on 2025 password management best practices to secure your data.
Advanced Tactics for Bulletproof Password Security

Using a password manager is a huge first step, but it’s not the whole story. If you really want to lock down your digital life, you need to start thinking like a security pro. That means adopting a few proactive habits that go beyond just storing credentials and focus on cutting off risk at every opportunity.
The core idea here is the principle of least privilege. It's a fancy term for a simple concept: only give people the absolute minimum access they need to do their job. Nothing more.
It’s just common sense. You wouldn't hand a house guest the master key to your home, car, and safe deposit box when all they need is to get into the guest room. The same logic applies online. If a team member just needs to post to social media, they shouldn’t have access to billing information or the power to delete the entire account. A solid password manager helps enforce this by letting you set view-only permissions or other specific restrictions.
Proactive Credential Management
Another critical habit is to treat all shared access as temporary. A massive security headache is "access creep"—that slow, silent accumulation of permissions by former employees, old contractors, and forgotten projects. It's a disaster waiting to happen.
The best way to fight this is by putting expiration dates on shared credentials from the very beginning.
- Contractors: If you bring on a freelancer for a three-month project, set their login access to automatically expire on their last day. No loose ends.
- Team Projects: Got a password specifically for a short-term marketing campaign? Schedule its access to shut off the day the campaign ends.
This isn’t about micromanaging; it’s about automating your security. You remove the chance of someone forgetting to revoke access later. For more tips on managing team access, our shared password management guide for teams is a great resource.
A password is a key. The more keys you have floating around, and the longer they work, the higher the chance one falls into the wrong hands. Limiting access duration and scope is non-negotiable for real security.
The Necessity of Regular Audits
Finally, you have to conduct regular access audits. This is your scheduled check-up to review who has access to what, ensuring your security setup still makes sense for your current needs. Think of it as spring cleaning for your digital accounts.
These audits are your best defense against password reuse, a shockingly common vulnerability. The numbers are pretty stark: while 89% of people know reusing passwords is a bad idea, only 12% actually use unique passwords for all their accounts. As a result, weak or stolen passwords contribute to nearly 49% of data breaches. You can see more on these password reuse statistics on huntress.com.
By embracing the principle of least privilege, setting expiration dates, and running regular audits, you shift from a reactive to a proactive security posture. It’s how you turn a simple password manager from a storage vault into a genuine security fortress.
What to Do When a Password Manager Isn't an Option

Look, a dedicated password manager is always the gold standard for sharing credentials. I'll recommend one every single time. But let's be realistic—sometimes it's just not practical.
Maybe you need to give a contractor one-time access right now, and they don't have a password manager. Or perhaps you're helping a less tech-savvy family member get into an account. In these moments, perfect security isn't the goal. The goal is harm reduction.
You're looking for a method that's worlds better than the absolute worst ways to share a password, like plain text or email. When the ideal solution is off the table, these are the next best things.
Use an Encrypted Messaging App with Disappearing Messages
Your first and best bet is a messaging app built on end-to-end encryption. Think of apps like Signal. Their entire design is centered on privacy, which means only you and the recipient can ever read the messages.
The key feature here is the ability to send disappearing or view-once messages. This is a game-changer for sharing something sensitive.
- You can set the password message to self-destruct after a set time or once it's been viewed.
- This prevents the password from just sitting in a message history forever, where it could be found later if the device is lost, stolen, or compromised.
It's the digital version of a self-shredding note. The information exists only as long as absolutely necessary and then poof—it’s gone. The only catch is that both you and the recipient need to have the same app installed.
Pro Tip: Never send the username and password in the same message. Send the username via the encrypted app, then follow up with the password through a completely different channel, like a quick phone call. This simple step of splitting the credentials makes an attacker's job much, much harder.
Try a One-Time Secret Sharing Service
Another fantastic, browser-based option is a "one-time secret" service. These are beautifully simple websites built for one specific task: sharing a piece of text that gets completely destroyed after being viewed just once.
The whole process couldn't be easier:
- You go to the website and paste in the password.
- The service generates a unique, secure link for you.
- You send that link to your recipient.
The moment they click the link and see the password, that data is permanently deleted from the server. If they try to click it again, or if someone else finds the link later, they'll just find an error page. It's a powerful and secure way to share a password that requires zero software installation, making it perfect for those urgent, one-off situations.
Answering Your Top Questions About Sharing Passwords
Let's be honest, trying to keep passwords secure can feel like a full-time job. Even when you're trying to do everything right, questions and doubts creep in. It's completely normal. Let's walk through some of the most common concerns I hear and clear up the confusion.
One of the biggest problems we all face is just the sheer number of passwords we're expected to remember. It’s not your imagination. The average person is juggling around 168 personal passwords and another 87 for their job. That's a staggering 255 credentials in total. This overload is why people take risky shortcuts—about 23% of us reuse passwords across different sites, and a worrying 20% don't bother with any security measures at all. If you're curious, you can dig into more of these password habit statistics at pandasecurity.com.
It’s this "password fatigue" that makes finding a secure sharing method so critical.
Is It Really That Bad to Send a Password in a Text?
I get this question a lot. The quick answer? Yes, it's that bad.
Standard SMS messages have no encryption, which means they're wide open to being intercepted. You might think, "What's the harm in texting the Wi-Fi password to a friend?" But it’s a slippery slope. The more you normalize sending credentials through insecure channels, the more likely you are to make a mistake with something far more important, like a bank or email password.
If you absolutely must use a messaging app, make sure it has two things: end-to-end encryption and a disappearing messages feature.
Can We Just Share One Master Password for Our Team’s Password Manager?
Please don't do this. It’s a common but incredibly risky shortcut that completely undermines the security of a password manager. Giving everyone the same master password creates a massive single point of failure. You lose all accountability—you have no idea who accessed what, when.
A password manager’s power lies in individual accountability. Every user gets their own unique master password. This is what allows for secure, controlled sharing of specific passwords through shared folders or vaults, without ever exposing the keys to the entire kingdom.
Think of it this way: sharing a master password is like making one copy of the master key to your office building and handing it out to everyone. If one person loses that key, your entire building is compromised. The right way to do this is to use the team and business features built directly into good password managers.
What Happens If I Forget My Master Password?
This is the number one fear that stops people from using a password manager, and it's a legitimate concern. Because these tools use a zero-knowledge security model—meaning not even the company can see your master password—they can't just send you a "reset password" link.
But don't worry, they've thought of this. Every reputable password manager has built-in recovery options.
- Recovery Kits: When you first sign up, you'll often be prompted to save or print a recovery kit or emergency sheet. Do it. Print it out and lock it away in a safe place, like a fireproof safe at home.
- Emergency Access: You can designate a trusted person—like a spouse, family member, or business partner—who can request access to your account. This usually involves a waiting period that you set, giving you time to deny the request if needed.
- Biometric Recovery: If you've enabled it on your phone, using your fingerprint or Face ID can often get you back into your vault.
The key is to set these recovery methods up before you ever need them. It takes just a few minutes, but it provides incredible peace of mind.
Ready to stop worrying and start sharing securely? AccountShare provides a platform where you can manage shared premium subscriptions with ease, built with security and convenience in mind. Discover a smarter way to share at https://accountshare.ai.
